Start researching smart home security topics on the web, and you quickly run into cover stories and reddit threads on smart home hacking. It's an unpleasant consideration: What if your new (and often expensive) smart home device gets hacked by a stranger? What could they do with it or the information it holds?
Smart home hacking has been a hot-button topic thanks to recent security breaches and general misinformation about this new type of technology many of us are living with.
At CNET, we aim to equip you with accurate, real-world information you can use to pick the best home security devices and keep your home safe. That also means understanding what smart home hacking really is, where it's likely to come from and how you can protect your devices. The good news is that your smart home tech is probably safer than you think, but let's take a deeper look.
How can smart home devices be hacked?
Let's cover a few important points: "Hackers" or to be specific, cybercriminals are not likely driving around scanning for vulnerable smart homes using nefarious gadgets. Wi-Fi ranges don't usually reach far enough for this to be effective and it would take a lot of effort for slim and spotty returns. There are some reports of major companies like casinos being hacked via smart devices, but very few of someone trying to Ocean's 11 residential homes.
Likewise, burglars interested in breaking into your house don't appear to be investing in the software or equipment needed to hack a smart lock first. There are very few reported cases of smart home security systems being hacked or electronically disarmed for petty theft. A low-tech approach is easier and more realistic. Most attempt to break unguarded windows or check for unlocked doors. So how do smart homes get hacked? Here are potential avenues of attack and how they work (or don't).
Widespread automated online attacks
These automatic online attacks from around the world that scan test nearly everything hooked up to the internet to see if accounts can be broken into, usually with brute-force password guesses that bombard devices with billions of various login attempts hoping one makes it through. Then the attack infects the device, adding it to a botnet for future cyberattacks or generalized data theft. A human cybercriminal rarely tries to seize control of your device. These mass online attacks are what created the often-cited Which? study about smart homes facing up to 12,000 hacking attempts per week (one succeeded, for an ieGeek camera).
This is an important reason to protect your account with updated passwords, but it doesn't mean anyone is purposefully targeting your smart home or that device security is weak. Bots are only fishing for whatever basic login vulnerabilities they can find on any available online system or account.
Phishing messages
It's not as common as other types of phishing, but some phishing emails or texts may pretend to come from your smart home security company. Giving them personal information like account logins or clicking their fake links (to malware designed to take over) may give cybercriminals access to devices they wouldn't otherwise be able to reach. And even generalized phishing attempts may lead criminals to your Wi-Fi network, through which they may be able to find and control connected home security devices.
Company-based data breaches
In this case, cybercriminals use brute force and similar attacks to target servers and networks where IoT companies keep information about smart home users in databases, including account login details, personal info about location and addresses, and camera footage stored in the cloud. It's a frequent target because data thieves could seize so much data at once, which is why you see headlines about major data breaches on a painfully frequent basis.
It's unlikely that the stolen data will lead to smart home device hacking, but it can put your accounts at risk and some cybercriminals may try to use that data however they can, which we'll get into more below.
Monitoring smart home data communications
As recently as the early 2020s, Internet of Things/smart home devices were found vulnerable to man-in-the-middle type attacks where criminals could spy on the data packets that smart devices were sending back to the internet. Smart devices send all kinds of data about their current settings and receive data back in return. With the right malware, a cybercriminal could potentially monitor this data and try to change or block it.
In practice, this simply doesn't happen. Criminals aren't in a position to do this to a smart home. Even if they were, today's smart home tech uses encryption practices and advanced protocols like Thread that make it useless. It's an example of how scary-sounding vulnerabilities don't actually make it into the real world.
Bluetooth malware
This type of malware, like the BlueBorne attacks, enters through a poorly secured internet connection and use Bluetooth capabilities to hack other devices, including phones and smart speakers. When these vulnerabilities became infamous in the late 2010s, companies quickly updated their security and Bluetooth encryption practices. We don't currently see many Bluetooth-based vulnerabilities (although some briefly crop up), and like man-in-the-middle attacks, they don't lead to smart home problems.
Who's trying to hack your smart home?
If burglars use the physical kind of brute force and black hat hackers are usually busy elsewhere, who exactly is trying to hack smart homes these days? Let's narrow it down to common culprits.
- A relation or acquaintance: Lots of troublesome smart home "hacking" comes from relations, exes, estranged roommates and others that already know the smart device logins or otherwise had access. They use that previous access to spy or cause trouble on purpose. That's a sign to update all login passwords and possibly file a police report.
- An untrustworthy company employee: Many home security data breaches come right from the company itself, usually in the form of an employee who's snooping through camera feeds like this ADT technician. As with interference from past acquaintances, little real hacking is required and the objective is usually more malicious or pervy than monetary.
- Data thieves looking to sell: These thieves are trying to scoop up as much personal data as possible, anything from addresses to login info, so they can sell those lists in the shadier parts of the internet. This data can be passed along to others who may try to use this data for select hacking attempts or resell it. This is why it's important to update your passwords when you're notified of a security breach.
- Potential blackmailers: The story goes that persistent cybercriminals attempt to seize control of smart home cameras and then threaten to do something unless you pay them. They may try to lock you out of your security system or claim they have compromising video footage of you. This is something of an urban myth: In most cases, people spam lies about a hack and hope someone will fall for it.
- Foreign governments: Government-backed entities aren't interested in spying on you personally, but they may want to collect as much information about other nations and their citizens' behavior as possible. That can sometimes lead to hacking attempts or security backdoors: Fortunately, the FCC currently keeps a list of companies that are prohibited from selling security devices in the US because of this risk (other countries have similar lists), including Huawei, Dahua and ZTE. Check these lists before buying foreign home tech products.
How do you protect against potential home security hacks?
- As you can see, while highly targeted attacks are unlikely, smart homes can be subject to broader hacking attempts. Fortunately, the vast majority of these attacks can be thwarted by basic security practices. Here are a few easy things you can do.
- Set strong passwords: Long, complicated passwords for your smart device app accounts and especially your Wi-Fi router are your best move against botnets and other online attackers. That doesn't have to be a headache these days, especially if you enlist a good password manager that generates strong passwords and save them for you for quick access.
- Enable two-factor authentication (TFA) whenever possible: More and more brands, like Ring and Blink, automatically use TFA to secure accounts during setup, which is a great step in the right direction.
- But trusted brands that use strong encryption: End-to-end encryption will go a long way toward protecting your data. Review security and privacy policies before making a final choice about a home security product. Arlo, a popular manufacturer of DIY home security devices, has healthy signs like penetration testing, third-party research, membership in the Connectivity Standards Alliance and details on their encryption practices.
- Store your data locally: If you're worried about wide-scale data theft, look for security devices that allow you to keep data off the cloud and company servers, including security cams from Lorex, Eufy and TP-Link Tapo cameras. On that note, consider keeping security cameras away from more private areas like your bedroom.
- Update your smart devices: Keep your apps and firmware consistently updated to patch any problems. Enable automatic updates if you can so you don't have to think about it. If you have a smart device that's several years old or older, it may be time to consider replacing it with a new model that's compatible with the latest protocols like Matter and Thread.
- Update your smart devices: Pay attention to your smart home security brands and if they face any security breaches, vulnerabilities or data theft. Stick with high-quality products from companies with a good track record.
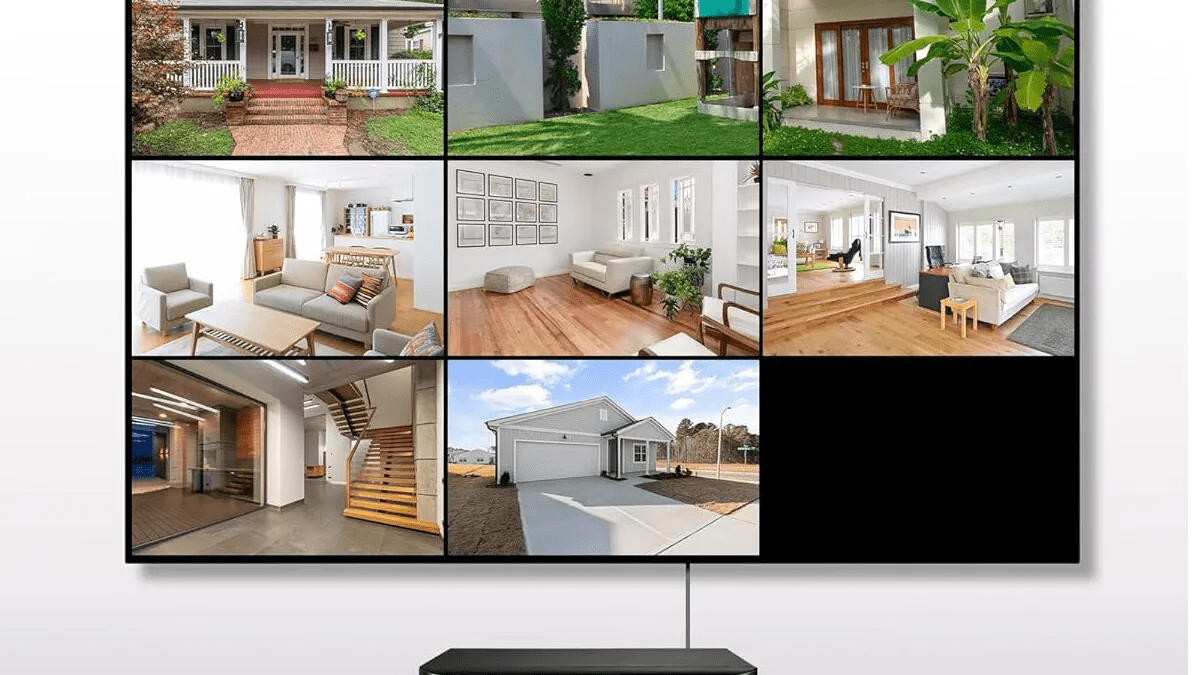
We'll keep you updated at CNET Home Security if we find serious problems with brand security and if any of our recommended companies have issues, like Wyze's repeated security mishaps that gave strangers a view into other people's homes.
Originally published in Cnet